Network segmentation
For maximum reliability, it is recommended that all independent systems in the network be strictly separated by virtual networks (VLANs ) and that their respective priorities be defined. This ensures that multiple technologies can coexist seamlessly on the same infrastructure without the risk of interference.
Why is network segmentation key?
-
Prioritizing critical data - Security systems (I&HAS) are extremely sensitive to delay (jitter) and latency. Proper VLAN configuration eliminates the risk of outages caused by normal network traffic.
-
Enhanced cybersecurity - By separating systems into isolated zones, you minimize the area of potential attack and prevent unauthorized access between subnets.
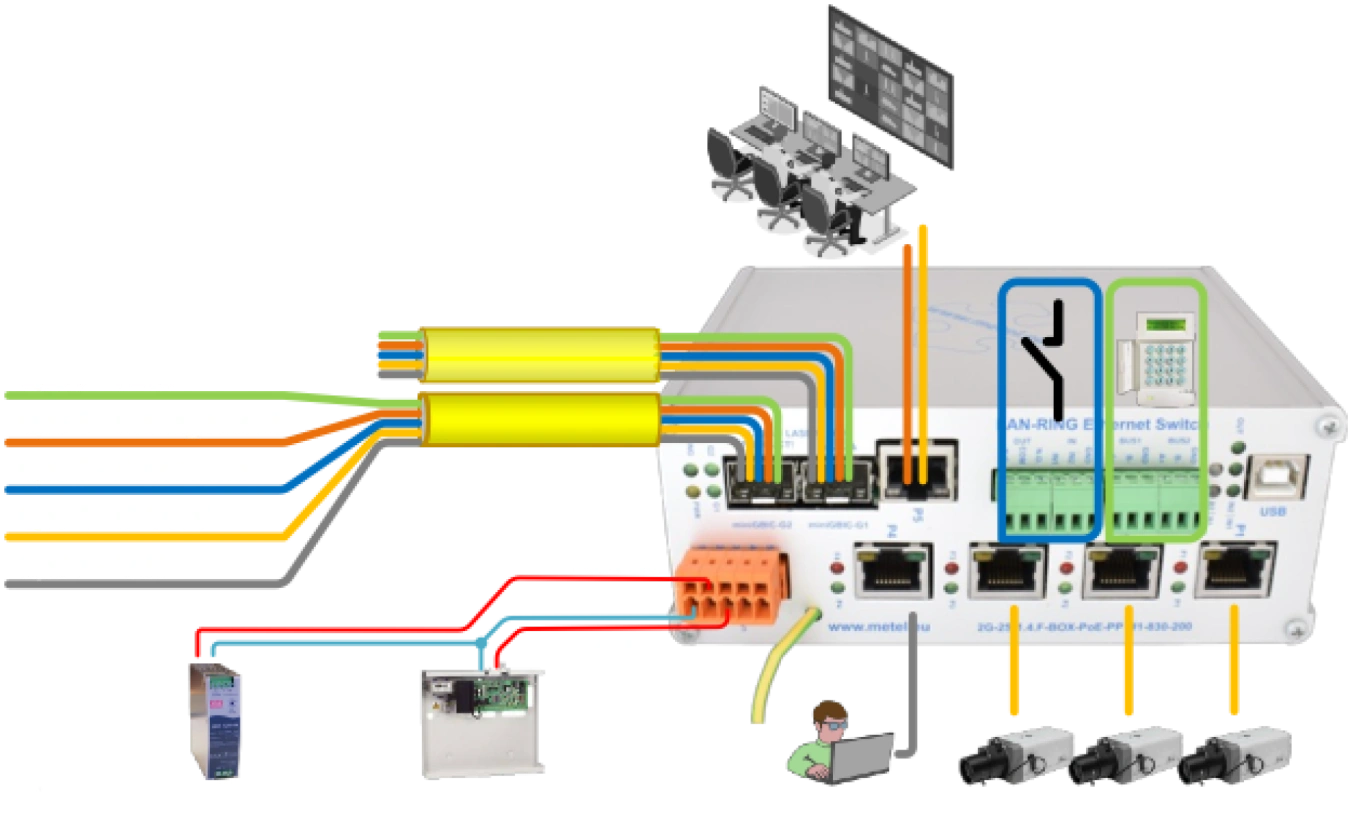
Unique advantage of LAN-RING switches
When using LAN-RING switches as a transmission path, you gain a major technological advantage. Our devices allow you to apply separate VLANs and priorities not only for standard Ethernet data, but also for:
-
RS485 bus data.
-
Signals from digital inputs and outputs.
As a result, alarm messages from the perimeter or sensors are transmitted with the highest priority, ensuring immediate system response even in a fully loaded network.
Recommended priority settings in a LAN-RING network
For optimal operation, we recommend dividing the data flows into the following classes according to the IEEE 802.1p standard:
|
Traffic Type |
Example Device/Bus |
Priority (CoS) |
Meaning |
|
Critical Alarms |
I&HAS (PZTS), RS485, Digital I/O |
7 (Highest) |
Immediate delivery regardless of network load. |
|
Control and monitoring |
Switch management, SNMP, SSH |
6 |
Stable access for managing and monitoring elements. |
|
Voice (VoIP) |
Intercoms, IP phones |
5 |
Priority transmission for clear audio without dropouts. |
|
Video (Real-time) |
IP cameras (live stream) |
4 |
Smooth video without jerks and delays. |
|
Normal data |
PC in office, printers, internet |
0 (Best effort) |
Standard operation with no priority requirements. |
Why use this setting?
- I&HAS Protection - The security system has the highest priority in the table(7). This means that even if someone on the network starts downloading large files or the video stream becomes overwhelmed, the alarm message gets priority in the LAN-RING switch and goes out first.
- Eliminate delays - For RS485 buses converted to Ethernet, it is crucial that packet drops are avoided. Prioritization ensures that serial data is not "queued" behind bulky video.
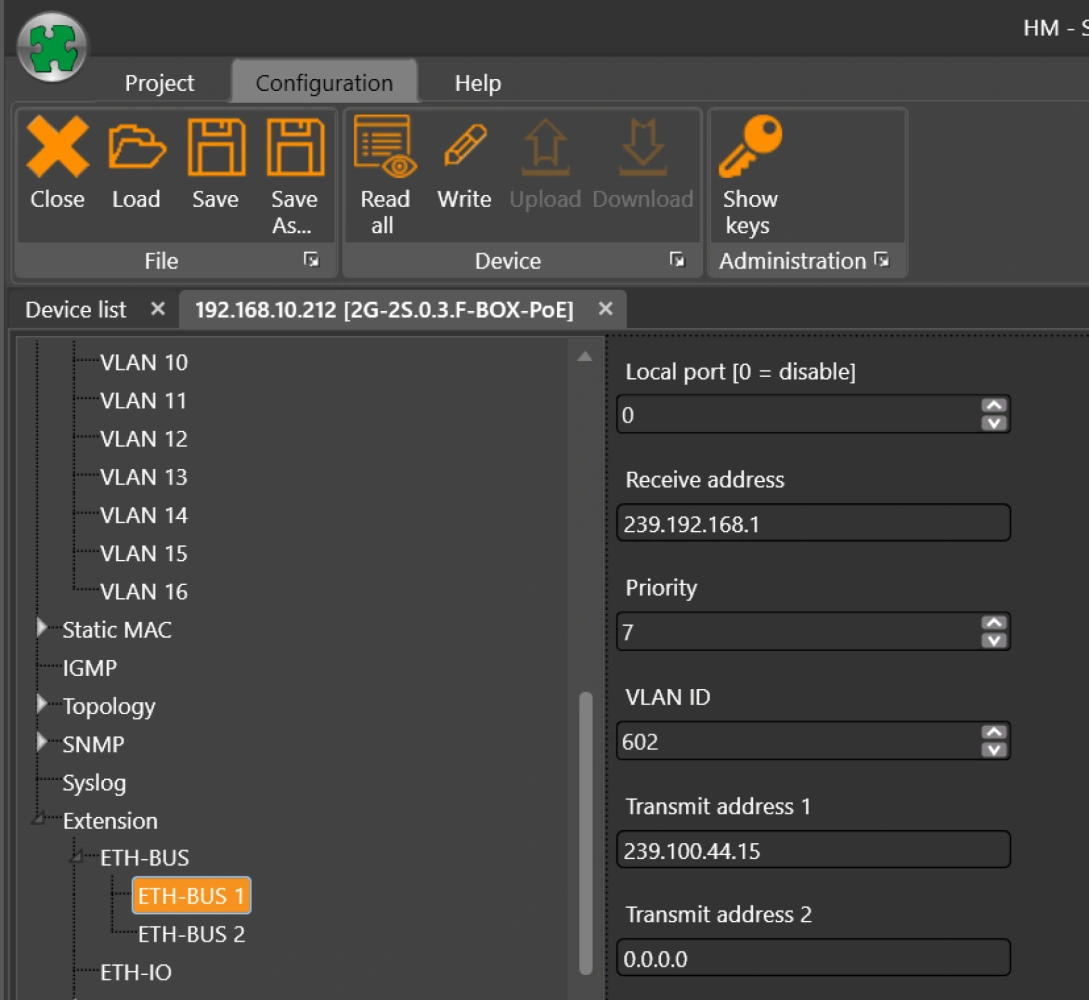
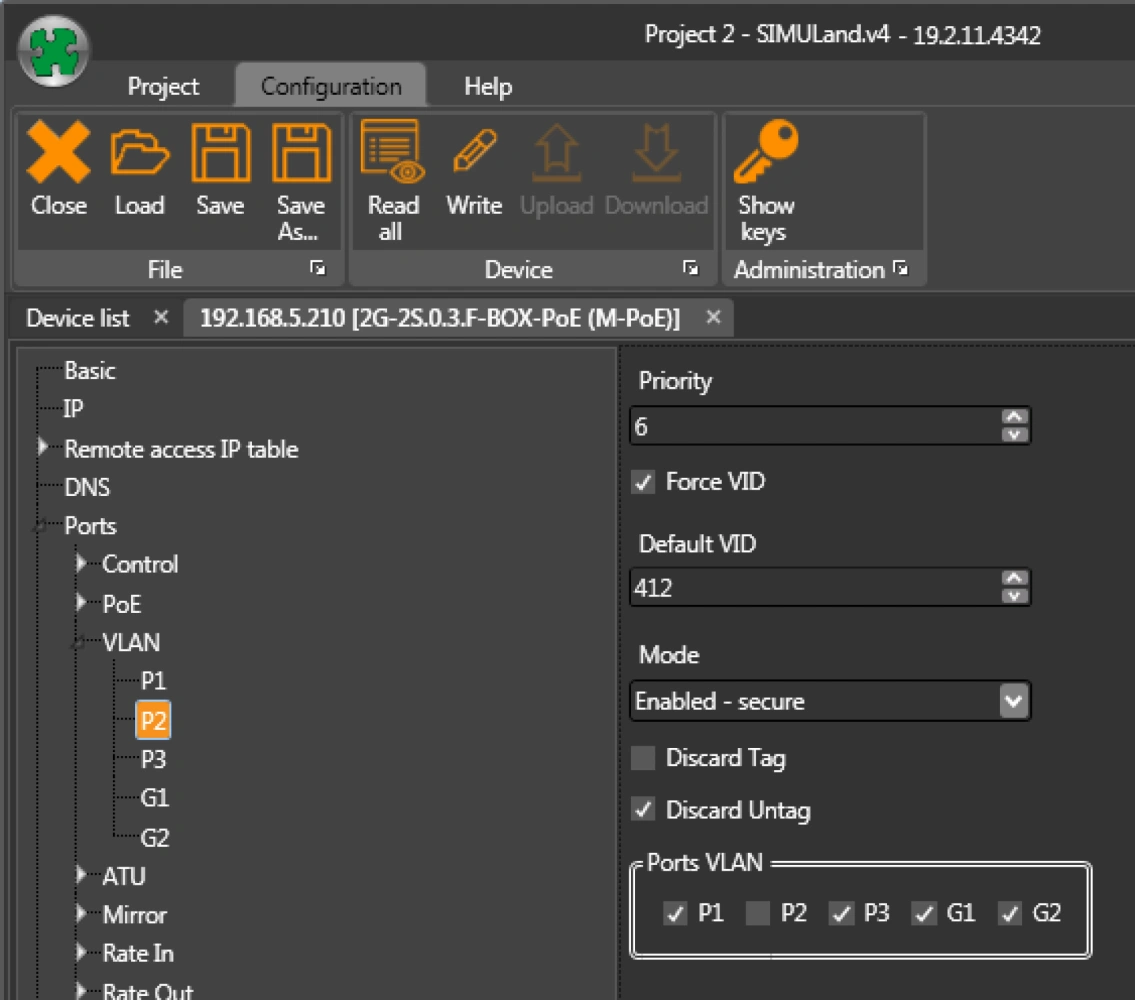
VLAN assignment and QoS priorities on the LAN port
VLAN and QoS priority assignment on RS485 port