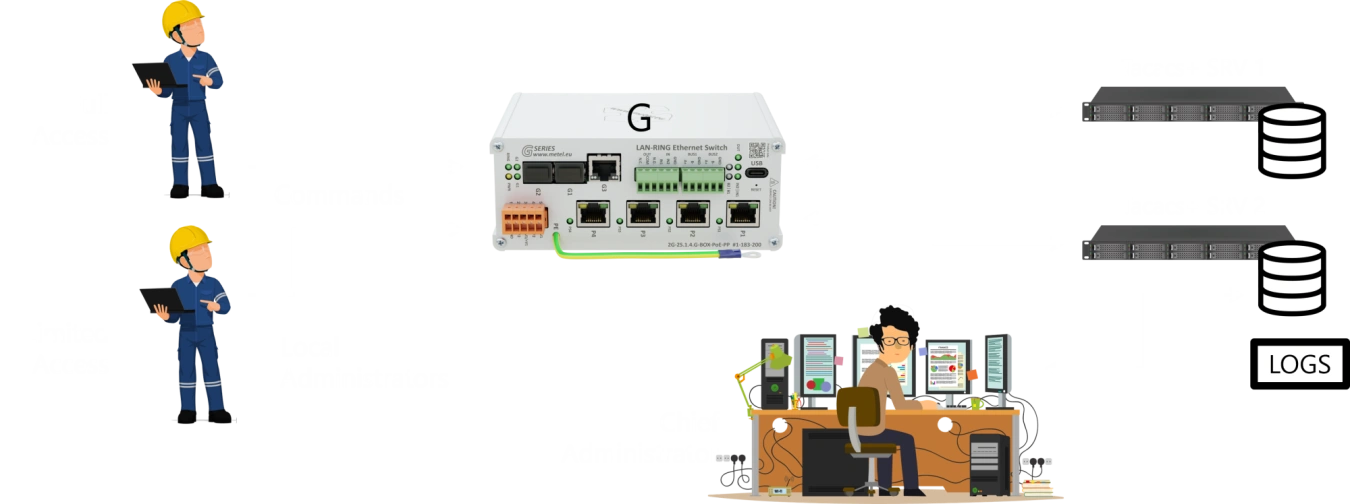
Centralised User Management
The G Series switches support user authentication through TACACS+. This security mechanism enables central management of user access and provides detailed control over authentication, authorization, and activity logging. With TACACS+ support, administrators can easily manage user permissions and ensure a high level of security for the network environment.
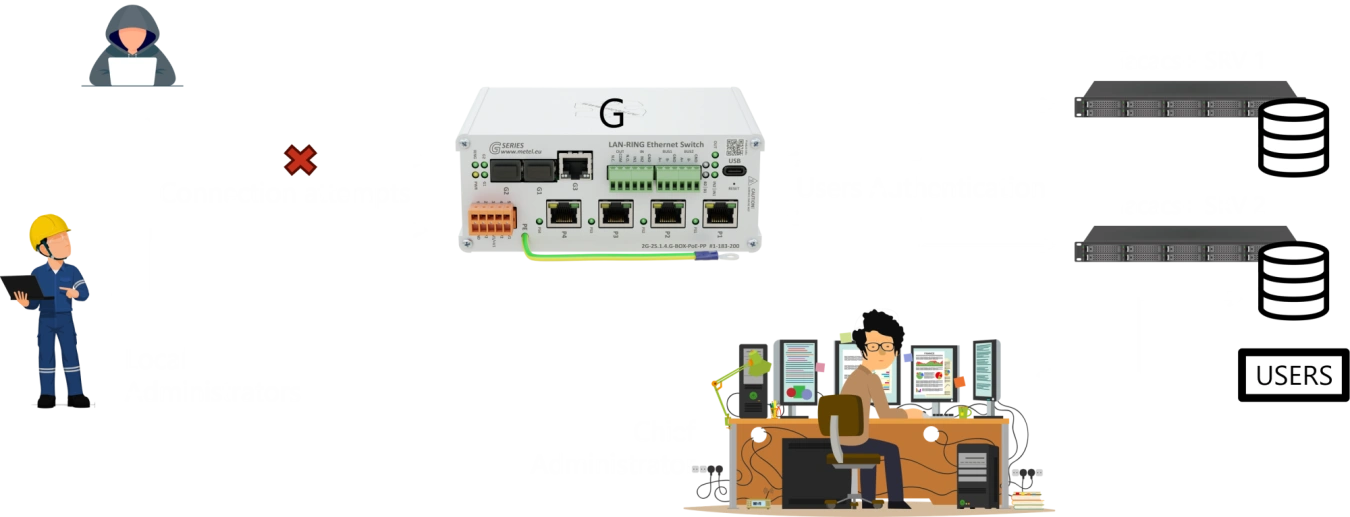
TACACS+ also allows users to be authorized to execute specific commands. This mechanism provides detailed control over what operations individual users can perform on the system, increasing security and reducing the risk of unauthorized interference. With this functionality, administrators can precisely define user permissions to ensure effective management of access rights in the network environment.

Last but not least, TACACS+ supports activity logging, which enables detailed tracking of all user actions in the system. This mechanism records logins, commands executed and configuration changes, providing administrators with important information for auditing and security analysis. Activity logging can effectively monitor access to network devices, identify unauthorized tampering, and provide a higher level of control and protection for the system.